Installing Nginx Proxy Manager
Introduction
So what is Nginx Proxy Manager. Well it’s a web frontend for managing a reverse proxy. Specifically Nginx Proxy Manager is made up of three components
- The web interface
- The backend web server (Nginx)
- A database for storage (embedded sqlite by default)
Combined, this provides a very easy way to manage, modify, and add services to your proxy without having to messing with configuration files.
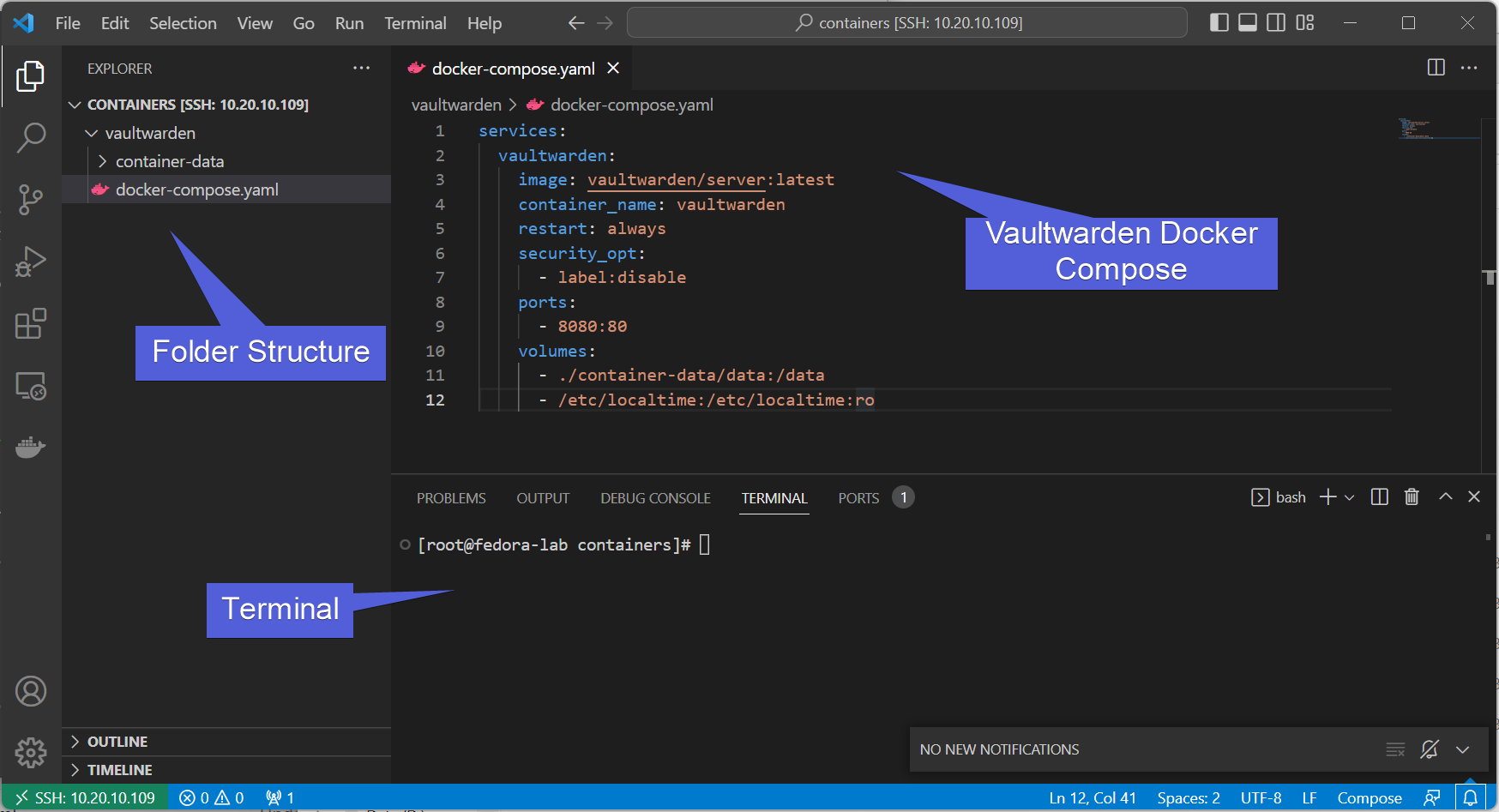
Looking at the Environment
We are using a Fedora 37 server running as a docker host with relevant data in /mnt/containers. We also have a web service (vaultwarden, but really it can be any web service) forwarded on port 8080.
Info
vaultwarden is a bitwarden compatible password manager, designed to work automatically with bitwarden extensions.
Info
This guide is representing the host using Visual Studio Code over SSH. You can read more on how that works here.
Awesome! Now how about our web service?
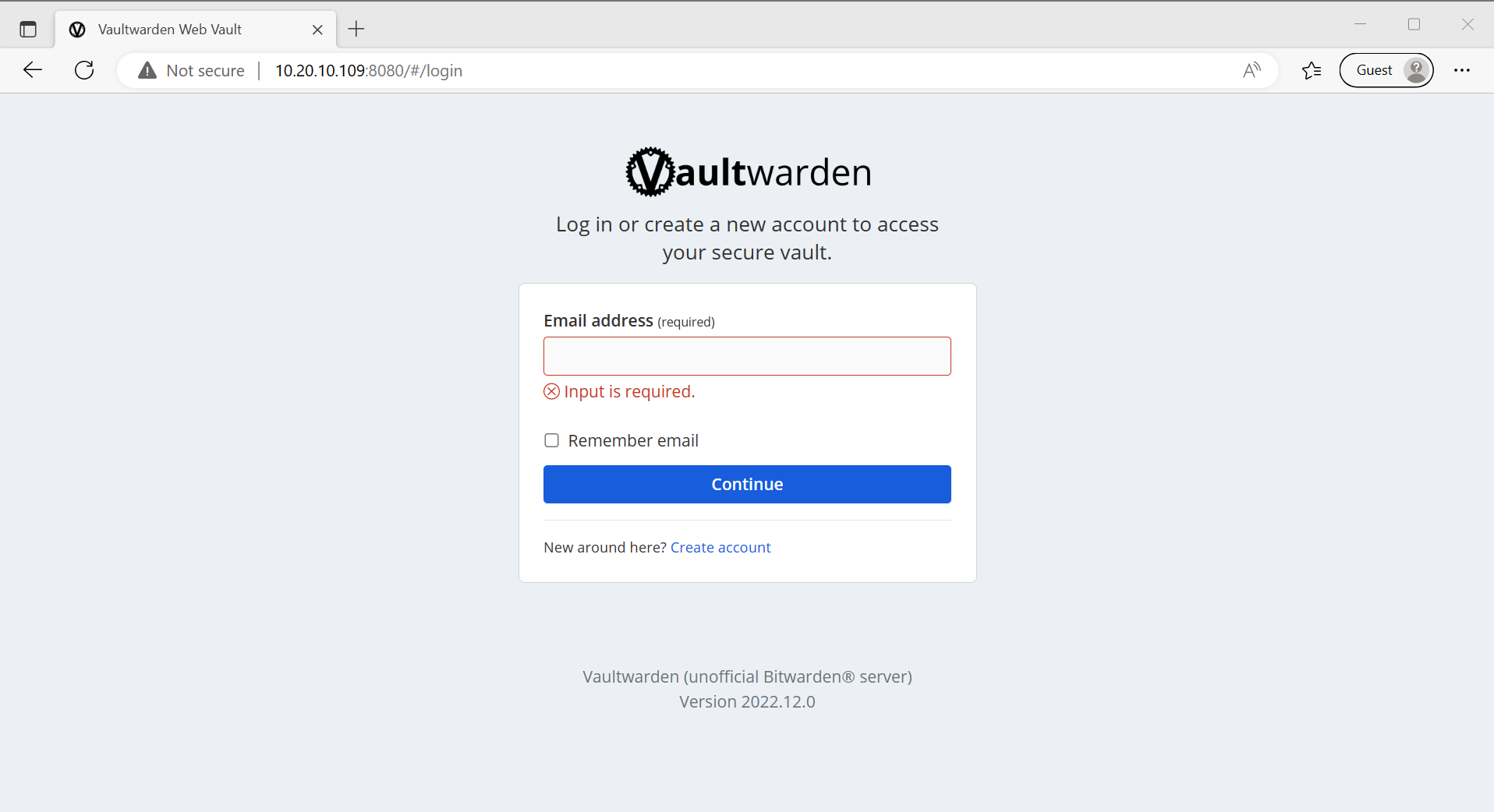
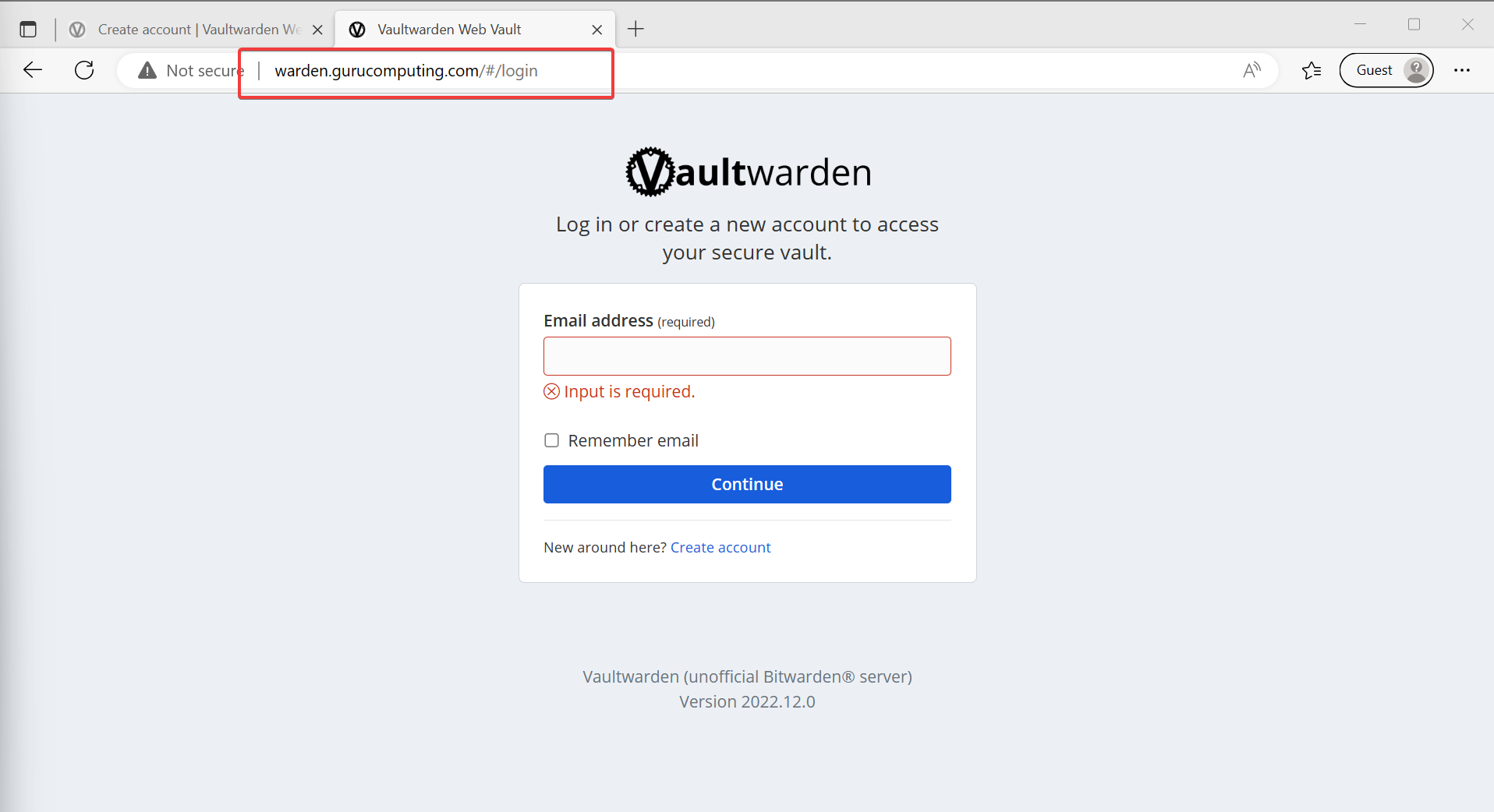
It’s working, but it’s being served on an IP and a port. Not ideal. It’s also not being served over HTTPS. Vaultwarden won’t even let you make an account without encryption (rightfully so):
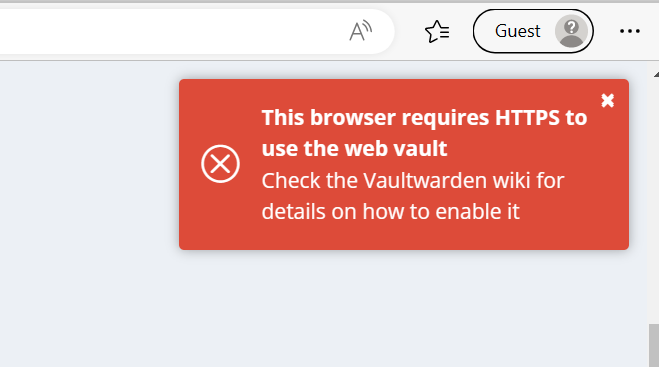
Let’s fix that.
Installing Nginx Proxy Manager
Alright, let’s actually get nginx proxy manager installed.
- Place the following
docker-compose.yamlin anginx-proxy-managerfolder:
services:
nginx-proxy-manager:
image: 'jc21/nginx-proxy-manager:latest'
restart: always
security_opt:
- label:disable
ports:
- '80:80' # Public HTTP Port
- '443:443' # Public HTTPS Port
- '8081:81' # Admin Web Port
volumes:
- ./container-data:/data
- ./certs:/etc/letsencrypt
Info
If you are wondering what label:disable does, it automatically sets SELinux folder permissions for volumes on a SELinux enabled distro, like fedora or centOS
- Bring it up with
docker-compose up -d
- If all goes well, you can browse to
<your-IP>:8081and manage your new installation!
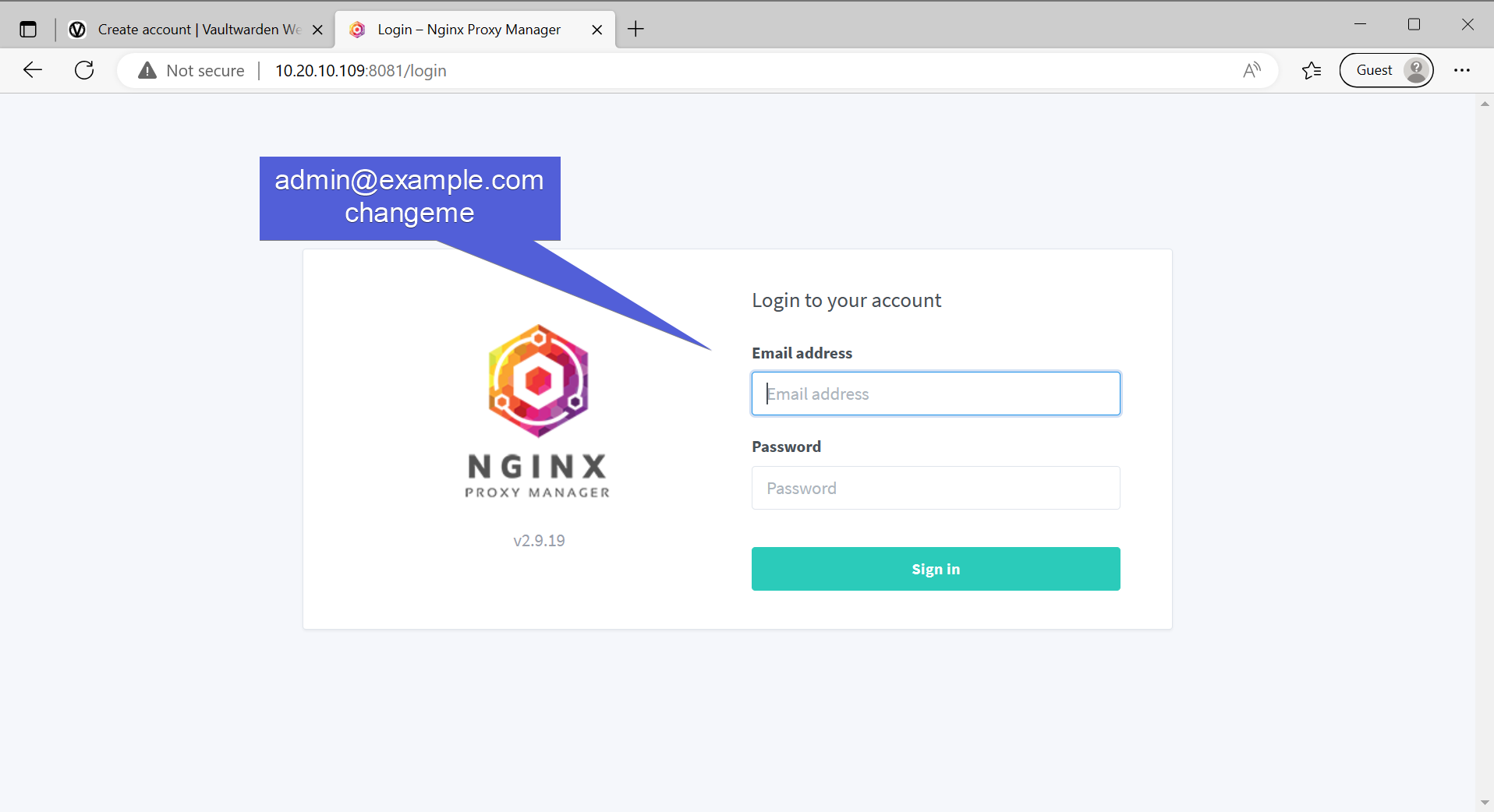
- Set up your details and save, and change your password while you’re at it.

.jpg)
Routing by Hostname
Before we go any further, we need to stop using IP addresses and start using DNS. This allows us to leverage a reverse proxy to route based on the URL. The DNS hostname can be defined in:
- Your current computer’s host file (no)
- Your upstream router (sure)
- Your Domain/DNS provider (sure if you want to get publicly valid certificates)
If you use OpenWRT (for example), you can do so in the latest version under hostnames.
- I am going to point my upstream router to route
warden.gurucomputing.comto my lab docker IP.

- Back to Nginx Proxy Manager, add a proxy host to route our
8080port.
- Attempt to navigate to
http://warden.<yourdomain>and if you’re configured right, you should be able to access vaultwarden by the URL!
Moving On
Alright, we’ve now managed to route a service by the URL (and potentially route many more services in the same fashion). However, we’re only halfway there. Let’s cover IP whitelisting, encryption, and leveraging docker networks in the next section.